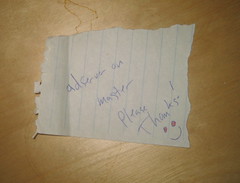
What is it? It's a small piece of the deployment system for the first amazon ad server. Brian and I worked on it together, along with a couple other amazonians, and we all sat on one hallway on the first floor of pacmed. I was probably out walking Declan when he pushed the latest ad server software and needed a sign off before it could go out, so he wrote this note and left it on my desk. Amazon basically has three levels of deployment. First there's a test server, where all the data is from the test domain. Then there's a "master" environment that this note refers to- and finally production. Code has to be signed off on by QA (that would have been me) on the test server and then on the master server again before it can be pushed.
I'm trying to remember how I let him know that I'd given my signoff... it was probably over email. I'm not sure that the ad server got an official sign off tracking form until it was a year or two old. You'll notice that at some point over the last seven years I doodled in red in the eyes of the smiley face. I have no idea when that was- possibly while I was running the preflight, waiting for something to load. I also noticed the "please" and "thanks" in this note - despite all the protests he'll give you, Brian is really a southern gentleman at heart.
This has brought back a lot of great memories from our initial launch of the ad server and the first year that it was up. Making apricot scones the weekend before launch for our Sunday AM bug bash. Our friend Greg, who was a web dev at the time, naming the templating language that we wrote ads in. (It's called "schusteranto" after Brian. Pretty cool that he has a programming language named after him, even if it is just an tiny substitution language.) Sitting directly behind PacMed's espresso stand, which was sooo handy sometimes. Declan learning how to play frisbee, instead of running away terrified from one when you tossed it. Walking home from work at 8 PM that summer, as the dotcom crash kept going, watching the sun setting while I walked up 2nd Ave. Seems like yesterday in some ways.

